NewNormal International – Blog
Addressing the Myth of Password Security in Business
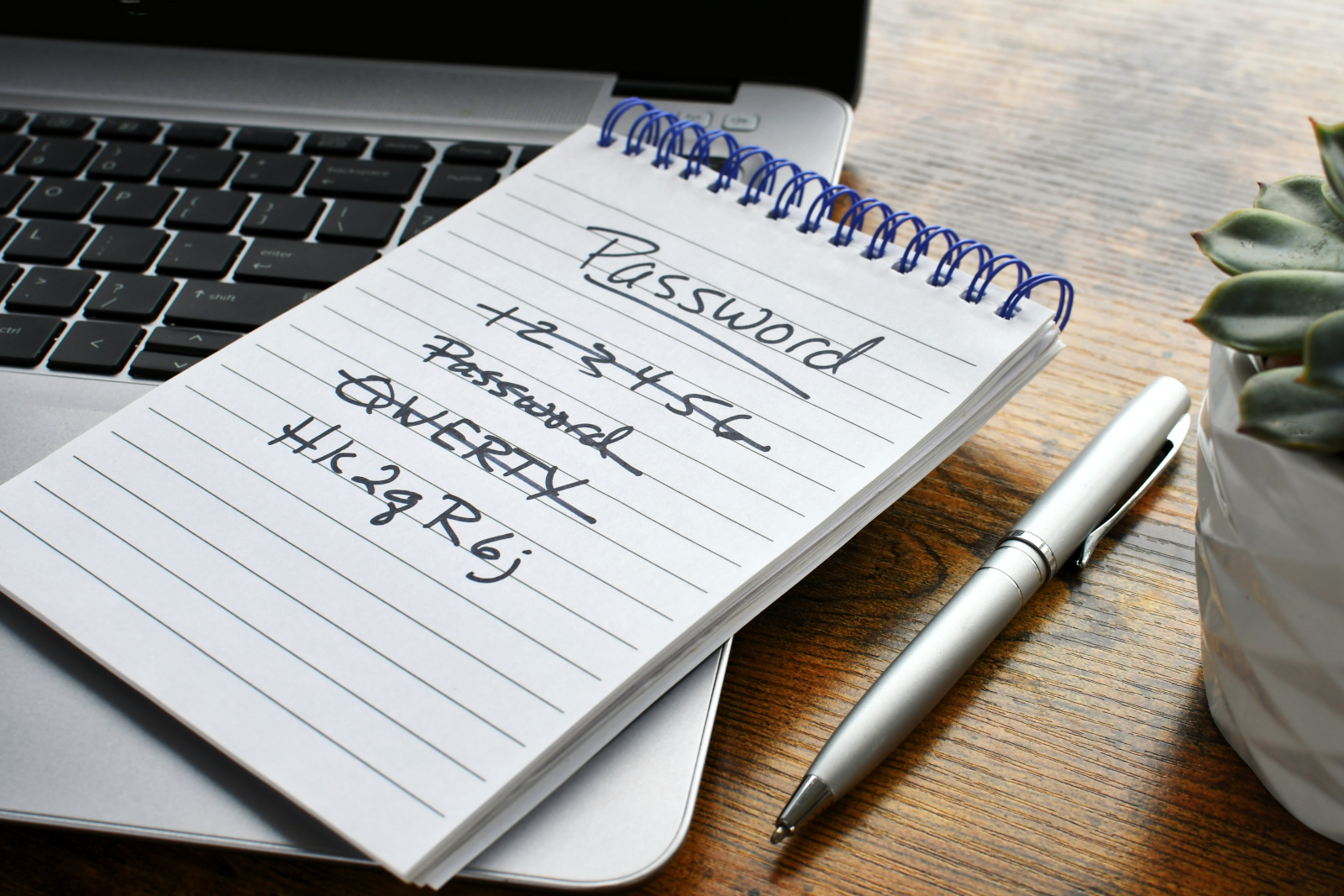
Combating False Security Perceptions in Cybersecurity “Users lull themselves in false Password Security in Business.” This statement sheds light on a critical issue in today’s digital business environment. In this…
Fortifying Business Resilience: Navigating Cybersecurity in Supply Chains and Cloud Computing
The Growing Threat to Supply Chains and Cloud Systems: Cybersecurity in Supply Chains and Cloud Computing In an era where cybersecurity in supply chains and cloud computing is a paramount…
Dark Clouds on the Workplace Horizon: Navigating Through Uncertain Times
Dark Clouds on the Workplace Horizon: Strategies for Business Resilience in Challenging Workplace Environments Dark Clouds on the Workplace Horizon symbolizes the current challenges and uncertainties businesses face. This article…
Creating a Digital Strategy: A Roadmap for Business Success
Essential Steps in Crafting an Effective Digital Strategy for Businesses In today’s fast-paced business environment, the question of “How is a digital strategy created?” is critical for executives, managers, and…
The Path to a Green Data Center: Pioneering Sustainable Business Practices
Embracing Eco-Friendly Solutions in Data Management The growing emphasis on sustainability has led businesses to consider The Path to a Green Data Center as a crucial aspect of their operations….
Status and Future of the Work Transformation
A recent IDC study on the digital workplace shows that two aspects are crucial for a functioning #WorkTransformation: The overall supervision of the network, application and hardware levels, as well…
More and more CDO Positions
Data is playing an increasingly important role for many companies. As a result, the role of the Chief Data Officer (#CDO) has slowly but surely become established in companies across…
How Legacy Software becomes a Nightmare
Many companies neglect their old software. It’s there anyway and has been doing its job faithfully and reliably for many years. What’s the big deal, it’s running, isn’t it? But…
New Wave of Cyberattacks
With the cyberthreats enterprises expect to face in the coming year and beyond, it’s time to dress warmly. Fortinet provides an assessment of how cold it could get on the…
Cloud Computing as a Key Technology of Digitalization
A hybrid cloud is a proven way for companies and organizations to drive digitization. But to make building a hybrid IT environment work, users need to consider several factors, from…